PenTester Nepal CTF Writeups#
This writeup covers two web challenges from PTN CTF, focusing on identifying and exploiting common web vulnerabilities including:
- SQL Injection
- Server-Side Request Forgery (SSRF)
- Command Injection
Challenge 1 – I Love Markdown#
Overview#
The challenge provided a web application that allowed users to convert Markdown files into PDF documents.
Key Observations#
- The platform allowed Markdown → PDF conversion
- The registration page was removed, leaving only a login interface
Initial Analysis#
Upon accessing the application, the only available functionality was the login page, and no credentials were provided.
This suggested that authentication might be vulnerable to SQL Injection (SQLi).

Initial Payload Testing#
Common SQL injection payloads were tested:
'
'-- -
'or 1=1--The application did not display SQL errors and instead returned Invalid credentials, indicating that SQL errors were likely suppressed by the backend.
Exploiting SQL Injection#
Further testing revealed that UNION-based SQL Injection was possible.
Payload used:
' Union select null,group_concat(username || ' : ' || password) from users--Explanation#
The backend database appeared to be SQLite, which uses the operator:
||for string concatenation.
The query returned usernames and passwords stored in the database.

Using these credentials allowed successful authentication into the web application.
Post-Login Functionality#
After logging in, the application revealed a Markdown to PDF conversion feature.
To analyze how the conversion worked, a sample PDF was generated and its metadata inspected.
The conversion tool used was wkhtmltopdf.

Identifying the Vulnerability#
The version of wkhtmltopdf in use is known to be vulnerable to Server-Side Request Forgery (SSRF).
Reference:
https://www.exploit-db.com/exploits/51039
Additionally, examining the HTML source revealed hints suggesting SSRF.
The backend server was running gunicorn, which by default listens on port:
8000
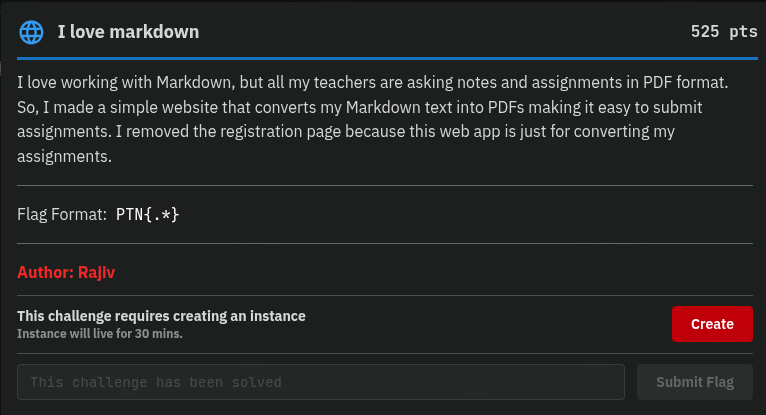
Exploiting SSRF#
Using the SSRF vulnerability in wkhtmltopdf, the following payload was embedded:
<iframe src="http://localhost:8000/hidden.html" width="800" height="200"></iframe>When the PDF was generated, the server attempted to render the internal resource.
This allowed retrieval of the flag.
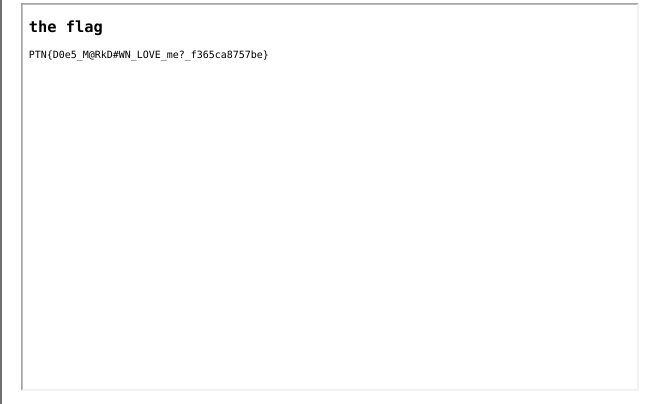
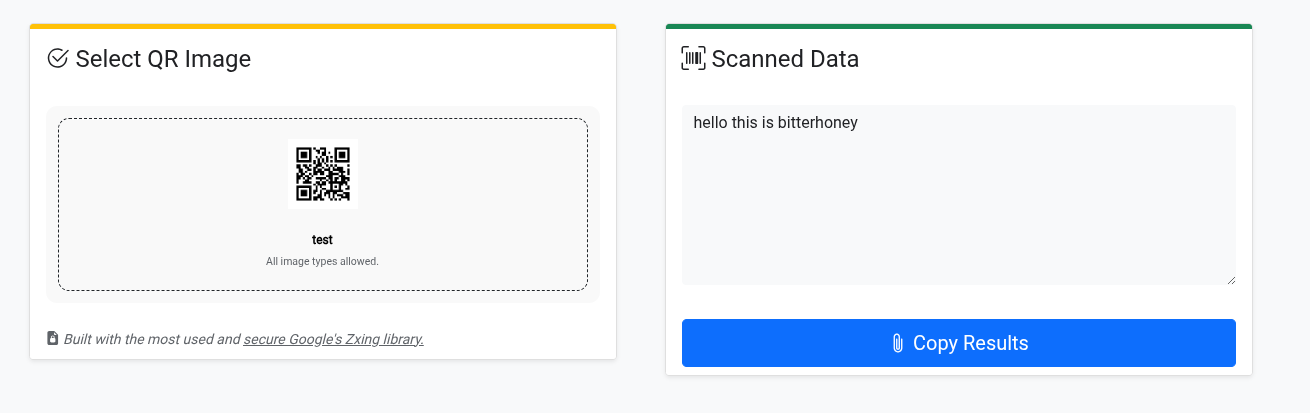
Challenge 2 – Simple QR#
Overview#
This challenge provided a web application that generates QR codes based on user input.

Initial Analysis#
The backend used Python and PHP, which suggested that functions like:
os.system()system()subprocess
might be used internally.
If user input was passed directly into these commands, it could lead to command injection.
Testing for Command Injection#
To test command execution, shell substitution techniques were used:
`command`$()
Test command:
`cat /etc/passwd`The command executed successfully, confirming that user input was passed directly to the shell.

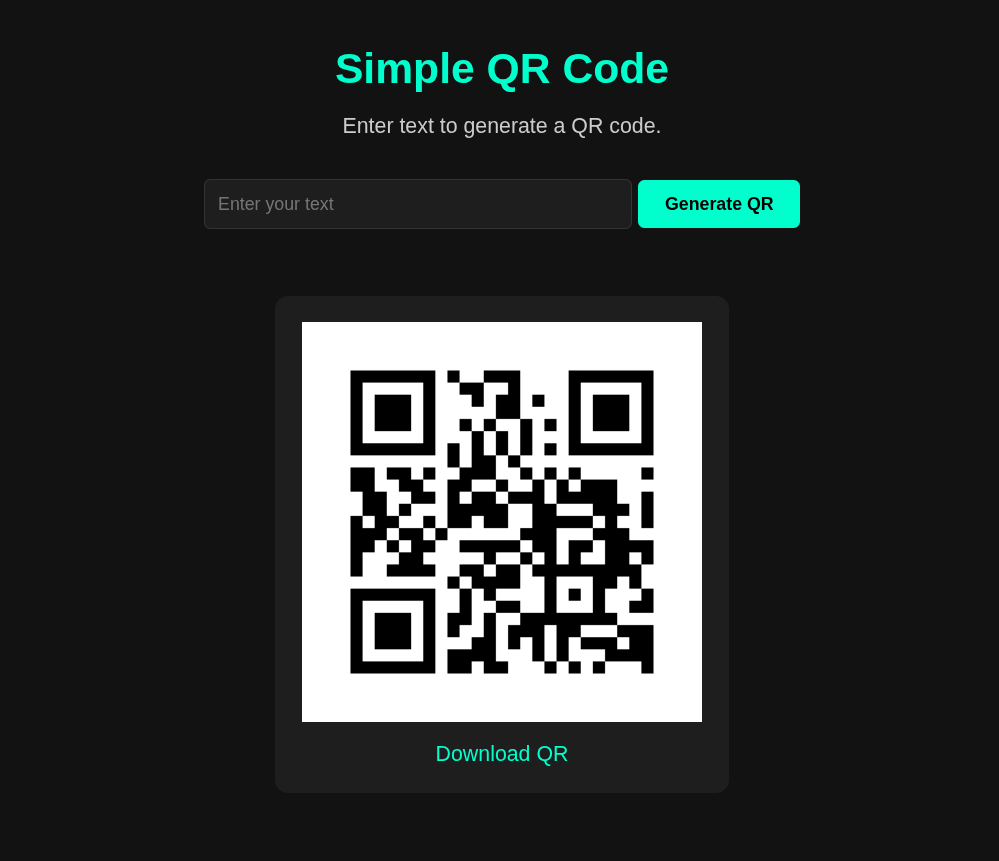
Retrieving the Flag#
Once command execution was confirmed, retrieving the flag was straightforward.
Payload used:
`cat /flag.txt`The output of the command was embedded into the generated QR code.
Scanning the QR code revealed the flag.

Conclusion#
These challenges demonstrated how multiple vulnerabilities can be chained together:
- SQL Injection → Credential extraction
- Authentication bypass
- SSRF via wkhtmltopdf
- Command Injection via QR generator
Key lessons:
- Validate user input
- Use parameterized queries
- Avoid executing shell commands with user input
- Sandbox external utilities like wkhtmltopdf
Thanks for reading this writeup, and good luck on your own hacking journey.